You May Have 5 Minutes To Patch Your Systems
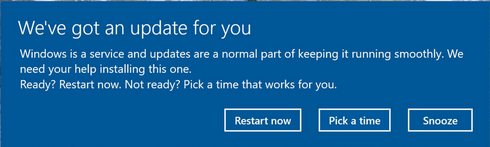
We’ve all been working on something on our device when we get a pop-up that a new patch or update is available, and we probably dismiss it as we want to stay in a flow state.
The most important term to remember after reading this article is what we call in the infosec community and Remote Code Executable, or RCE. What this means is someone has found a way to remotely run code on your device(s) without your consent.
Another term that is worth remembering is a “zero day” which means that as an industry, there’s been 0 days since the vendor has offered a patch to their software to protect you from being exploited. Most software updates are not critical updates like RCEs or zero days, so if you keep delaying the patch or update for a few days, you’ll likely be OK, but I’m writing this to encourage you to be sure, moving forward, as we are breaking some record ground on zero days this year, likely thanks to the automation capabilities of AI of the last year.
There have been a few major zero days in the last week as an example, most notable was BLASTPASS as disclosed by my friends at Citizen Lab, which was a chain of exploits that could compromise even the latest iphones without any interaction from the victim.
Another major zero day this week, also disclosed by Citizen Lab, was able to impact anyone using Mozilla Firefox web browser, or Mozilla Thunderbird client. This means that when the exploit, or zero day was announced, Mozilla was not yet aware of the issue or had not yet made a patch available, so all customers had no way to protect themselves until a patch was a released – a busy day for the Mozilla security team I’m sure!
So why am I writing this article? I was once on the team responsible for patching the one of the largest companies in the world, we had well over 100,000 employees at the time, so you can imagine the device landscape … managing this was a nightmare, and patching sadly isn’t much better today, decades later – not just from a technical perspective, but also from a social perspective.
What do I mean by social perspective? I wish more people were aware of the difference from a critical (install now!) update and a feature update. On the critical side of things, check out Robert Graham’s masscan which I’ve been warning people about for about a decade since it came out. What this software does is once an attacker gets access to a zero day exploit and/or RCE, they can use this free to download tool called masscan to scan the entire internet (IPv4 TCP for the nerds and critics reading this) in under … 5 minutes!
So what does this mean to the average computer user? Imagine Apple sent out a security update to update your iphone over the last week, and you choose to ignore it and have it install the patch over night instead when it would be more convenient for you – anyone malicious and with the right resources can get access to this zero day code, scan the entire internet in 5 minutes, getting access to your iphone in less than 10 minutes, as well as the other iphones out there connected to the internet. It probably would have been worth it to just to the update at the time, instead. As an aside, if you’re an iphone user, you might also be interested in Lockdown mode, but I digress…
I’ve wanted to write this article for some time, and I hope that after reading it, you should hopefully at least pause to check the next time any of your software prompts you for an update, to check to see if it’s an RCE, and if so, I would not hesitate to update asap!
While I have you reading on the topic of software patching, assuming you’re not that technical and like learning these things, this is not the same as say an operating system update to the latest version, as this update might just be an upsell, or new features, in which case updating may have the opposite issue, as updating an operating system or complete new version of software (based on new features, not security updates!) could introduce new software bugs onto your device, so in that case, I usually wait a few weeks until most of the big/obvious bugs have been fixed.
To summarize and simplify the next time you get offered a new software update or patch:
- Click on the update or patch details, just to find out if it’s a security update, and if so, understand how critical this patch is, most patches or Common Vulnerabilities and Exposures (CVEs) will explain this to you.
- If it’s an RCE, update immediately. If it’s a security only patch, probably not a terrible idea to update right away as well.
- If it’s not a security update, over night is likely fine if you want to maintain your flow state with what you were working on when you got the prompt.
- If it’s a software update or new feature updates with no relation to security, a week might be OK, based on your risk tolerance.
About Kris: For over 20 years I’ve been involved in helping organizations develop and implement patching strategies, from multi-nationals, to SMEs and non-profits. I also offer myself as a replacement to University to those eager to get into the infosec world, based on their skills and interests, as well as demand from the industry.